- John The Ripper Mac Os X Free Download
- Mac Dvd Ripper
- John The Ripper Mac Install
- John The Ripper Mac Tutorial
DO NOT USE THIS VIDEO TO BRAKE INTO ACCOUNTS! I MADE THIS VIDEO SO YOU CAN LEARN HOW TO USE JOHN THE RIPPER. Links: John The Ripper: http://www.openwall.com/.
John the Ripper Pro for Mac OS X features a native package (dmg), universal binary, support for SSE2 and AltiVec acceleration (on Intel and PowerPC, respectively), a large multilingual wordlist. How To Install JTR on a Mac. John The Ripper is a cracking password program, also known as JTR or john. John The Ripper is not for the beginner, and does NOT crack WPA (alone) (by itself) (solely). You must be able to use Terminal, there is no GUI. New in John the Ripper 1.7.9: Added optional parallelization of the MD5-based crypt(3) code with OpenMP. Added optional parallelization of the bitslice DES code with OpenMP.
John The Ripper is a password cracking tool. Compiling it for Mac was working fine until Apple removed the openssl headers. Here are instructions for building John The Ripper on OS 10.11 El Capitan.
I’m assuming you know how to run some basic shell commands in Terminal. If you don’t know what that is, and don’t know how to get a shell, then this won’t make much sense to you!
Before you begin, ideally, you should get all the tools you need to compile things on your mac. You might need to get XCode (from the App Store) and install the command-line tools. If you’re not sure whether the tools are installed or not, get a terminal running and execute the command ‘cc’:
If you get a clang error message (this is good!) you have the tools, you have the talent; it’s Miller time!
If you don’t have the tools installed, you’ll get a pop-up window that asks if you want to install the command-line tools.
For this walkthrough we’ll download everything in to /tmp so my instructions can make use of absolute paths when making and patching JtR. If you downloaded elsewhere, just make a note of the directory.

This has been tested and is working on a freshly installed Mac OS 10.11.3 with only the X-Code and the command line tools installed.
Ok, let’s go!
First, identify your version of openssl to make sure we get the same header source code as the installed version. It should be the same on all the El Capitans, but just to be sure, open a terminal and run the following and make note (mine is 0.9.8zg):
Download the openssl source from http://openssl.org/ – this will provide you with the missing header files – if you aren’t using 0.9.8zg, go to the http://openssl.org/ site and find the correct source download for your version!
Get and unpack the John The Ripper (JtR) source from openwall.com:
The makefile that was included with john-1.8.0-jumbo-1 is missing some bits, read the patch if you want to know more:
Tell JtR configuration where to find the OpenSSL you downloaded.
If you don’t get any errors, you’re (probably) done!
The files for your JohnTheRipper are in /tmp/john-1.8.0-jumbo-1 and the executable files are in the subdirectory labelled ‘run’. Test it out by doing:
If you get a bunch of output, then it compiled!
Remember to move your /tmp/john-1.8.0-jumbo-1 directory somewhere OUT of tmp if you decide you want to keep it. e.g. To move it to your home directory do:
If you want to temporarily add it to your path so you can just run the commands from anywhere, do:
Happy cracking!
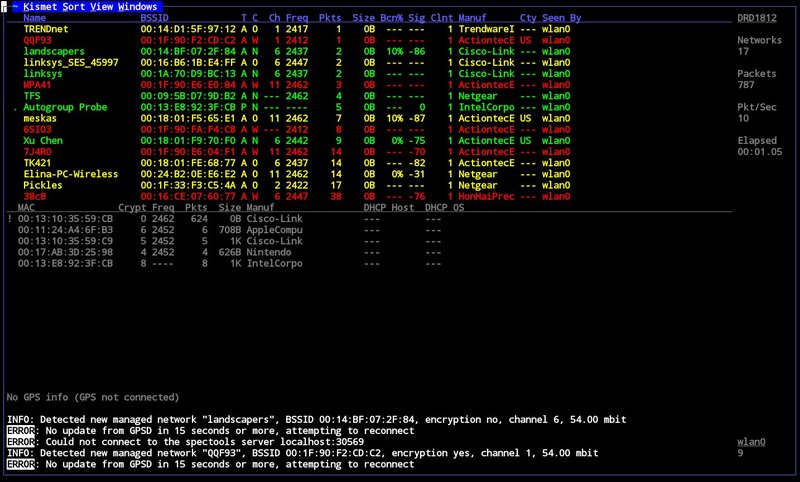
John the Ripper (JtR) is one of the hacking tools the Varonis IR Team used in the first Live Cyber Attack demo, and one of the most popular password cracking programs out there. In this blog post, we are going to dive into John the Ripper, show you how it works, and explain why it’s important.
Notes about hacking: Hacking is a pursuit of knowledge about systems, design, and humans. In this case, we are talking about software and operating systems.
Get the Free Pen Testing Active Directory Environments EBook
Hacking is not necessarily criminal, although it can be a tool used for bad intentions. We advocate for ethical hacking. Stay in the light side of the Force.
How Does John the Ripper Work?
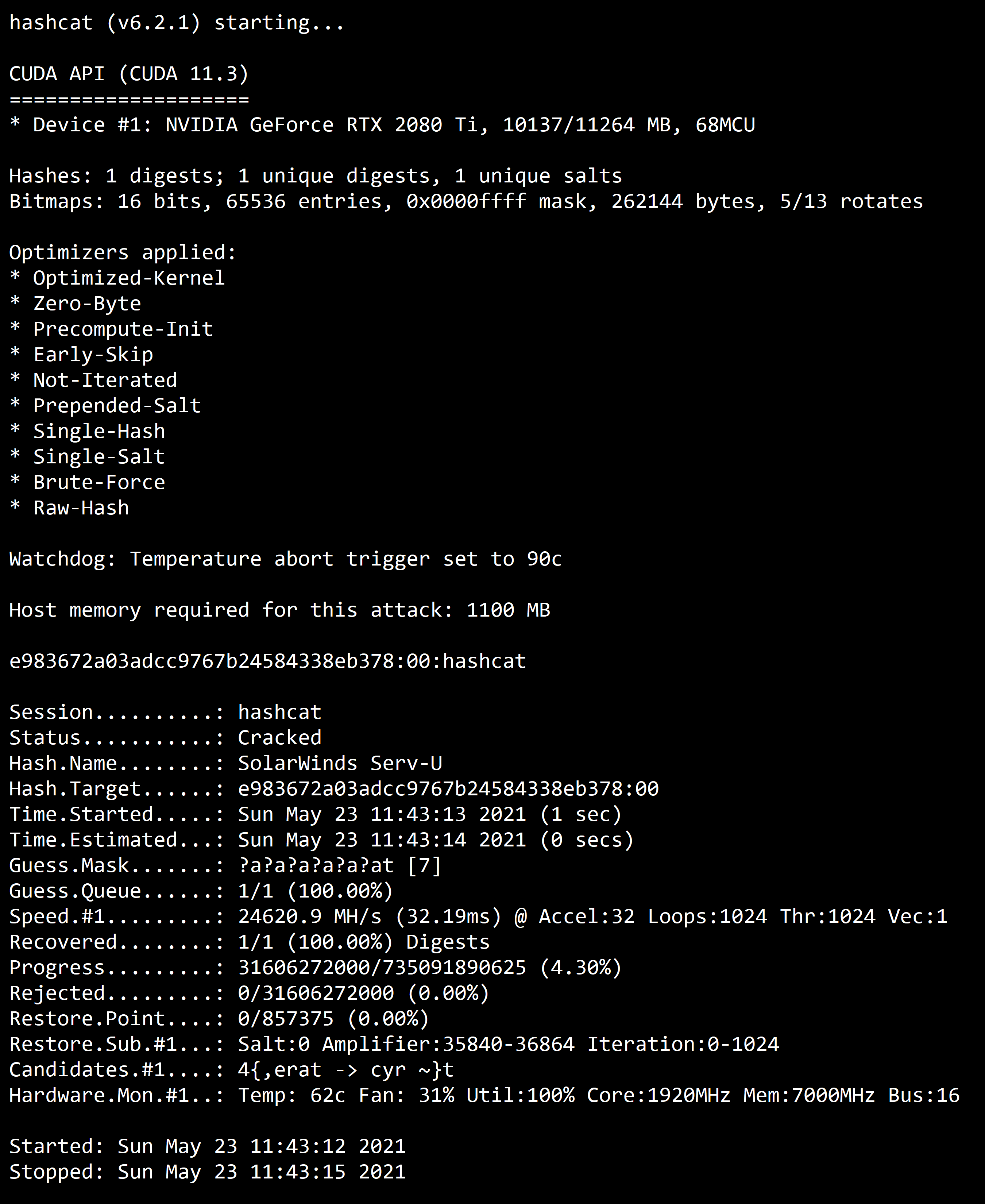
JtR supports several common encryption technologies out-of-the-box for UNIX and Windows-based systems. (ed. Mac is UNIX based). JtR autodetects the encryption on the hashed data and compares it against a large plain-text file that contains popular passwords, hashing each password, and then stopping it when it finds a match. Simple.
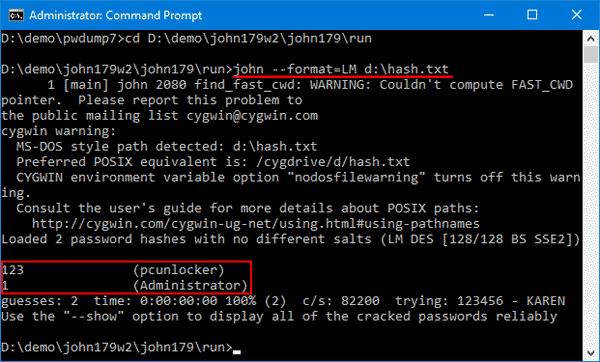
In our amazing Live Cyber Attack demo, the Varonis IR team demonstrates how to steal a hashed password, use JtR to find the true password, and use it to log into an administrative account. That is a very common use case for JtR!
JtR also includes its own wordlists of common passwords for 20+ languages. These wordlists provide JtR with thousands of possible passwords from which it can generate the corresponding hash values to make a high-value guess of the target password. Since most people choose easy-to-remember passwords, JtR is often very effective even with its out-of-the-box wordlists of passwords.
JtR is included in the pentesting versions of Kali Linux.
What is John the Ripper Used for?
John The Ripper Mac Os X Free Download
JtR is primarily a password cracker used during pentesting exercises that can help IT staff spot weak passwords and poor password policies.
Here is the list of encryption technologies found in JtR:
- UNIX crypt(3)
- Traditional DES-based
- “bigcrypt”
- BSDI extended DES-based
- FreeBSD MD5-based (linux and Cisco IOS)
- OpenBSD Blowfish-based
- Kerberos/AFS
- Windows LM (DES-based)
- DES-based tripcodes
- SHA-crypt hashes (newer versions of Fedora and Ubuntu)
- SHA-crypt and SUNMD5 hashes (Solaris)
That’s the “official” list. JtR is open-source, so if your encryption of choice isn’t on the list do some digging. Someone might have already written an extension for it.
Mac Dvd Ripper
How to Download John the Ripper
JtR is an open-source project, so you can either download and compile the source on your own, download the executable binaries, or find it as part of a penetration testing package.
The official website for John the Ripper is on Openwall. You can grab the source code and binaries there, and you can join the GitHub to contribute to the project.

JtR is available on Kali Linux as part of their password cracking metapackages.
Tutorials for Using John the Ripper
We are going to go over several of the basic commands that you need to know to start using John the Ripper. To get started all you need is a file that contains a hash value to decrypt.
John The Ripper Mac Install
If you ever need to see a list of commands in JtR, run this command:
Cracking Passwords
John the Ripper’s primary modes to crack passwords are single crack mode, wordlist mode, and incremental. The single crack mode is the fastest and best mode if you have a full password file to crack. Wordlist mode compares the hash to a known list of potential password matches. Incremental mode is the most powerful and possibly won’t complete. This is your classic brute force mode that tries every possible character combination until you have a possible result.
The easiest way to try cracking a password is to let JtR go through a series of common cracking modes. This command below tells JtR to try “simple” mode, then the default wordlists containing likely passwords, and then “incremental” mode.
You can also download different wordlists from the Internet, and you can create your own new wordlists for JtR to use with the –wordlist parameter.
If you want to specify a cracking mode use the exact parameter for the mode.
Word Mangling Rules
Mangling is a preprocessor in JtR that optimizes the wordlist to make the cracking process faster. Use the –rules parameter to set the mangling rules.
Viewing Your Output
When you want to see the list of passwords that you have cracked, use the –show parameter.
If your cracked password list is long, you can filter the list with additional parameters. You can also redirect the output using basic redirection in your shell. For example, if you want to see if you cracked any root users (UID=0) use the –users parameter.
John The Ripper Mac Tutorial
Or if you want to show users from privileged groups use –groups.
Below is the JtR command from our Live Cyber Attack Webinar. In this scenario, our hacker used kerberoast to steal a Kerberos ticket granting ticket(TGT) containing the hash to be cracked, which was saved in a file called ticket.txt. In our case, the wordlist used is the classic rockyou password file from Kali Linux, and the command was set to report progress every 3 seconds.
If you want to see some cool pentesting and defense tactics using Varonis, check out the Live Cyber Attack Webinars! Pick any time that works for you!